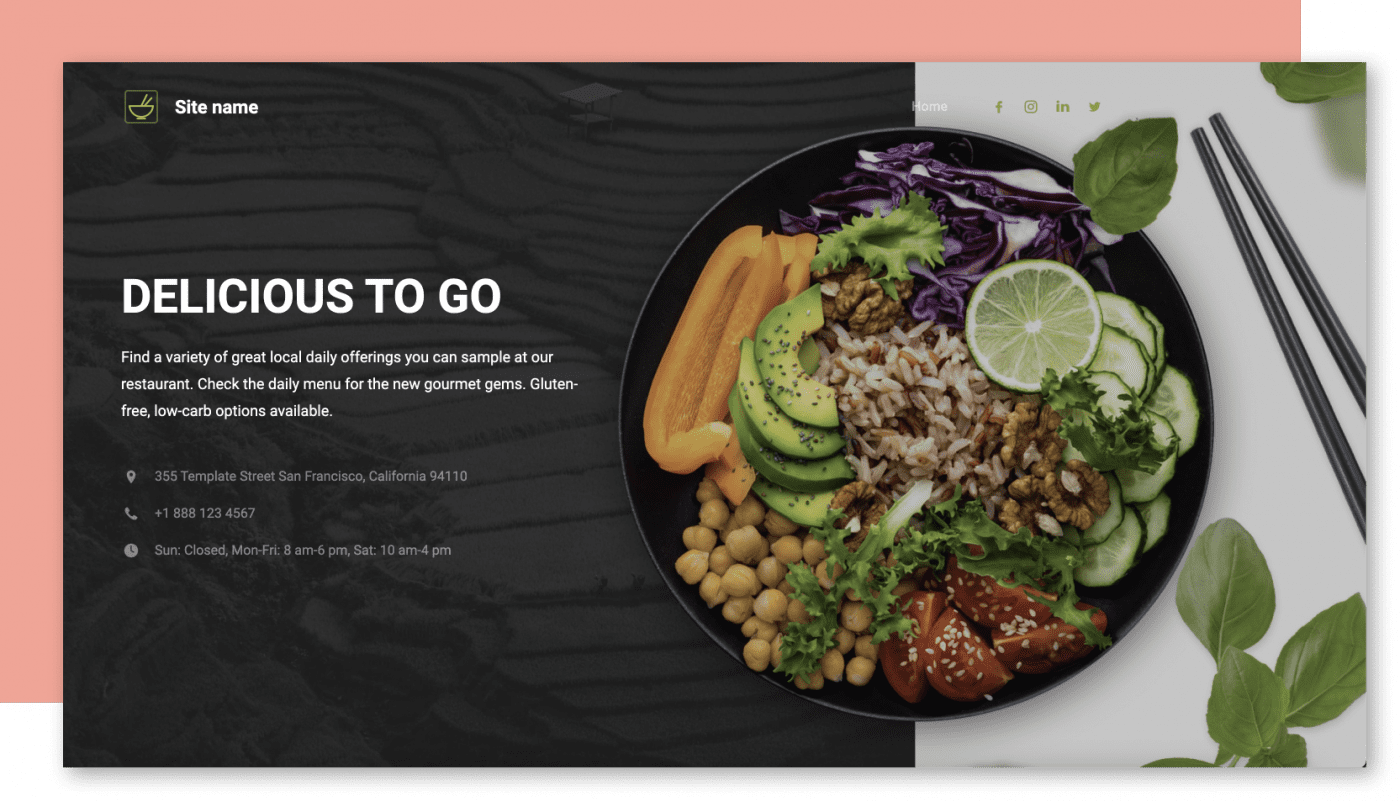
One-Stop Shop For Small Businesses. Web Design Without the Gimmicks. Create the website you’ve always dreamed of. Hostway's web design services empower you to effortlessly build the beautiful, modern website you deserve without the stress.
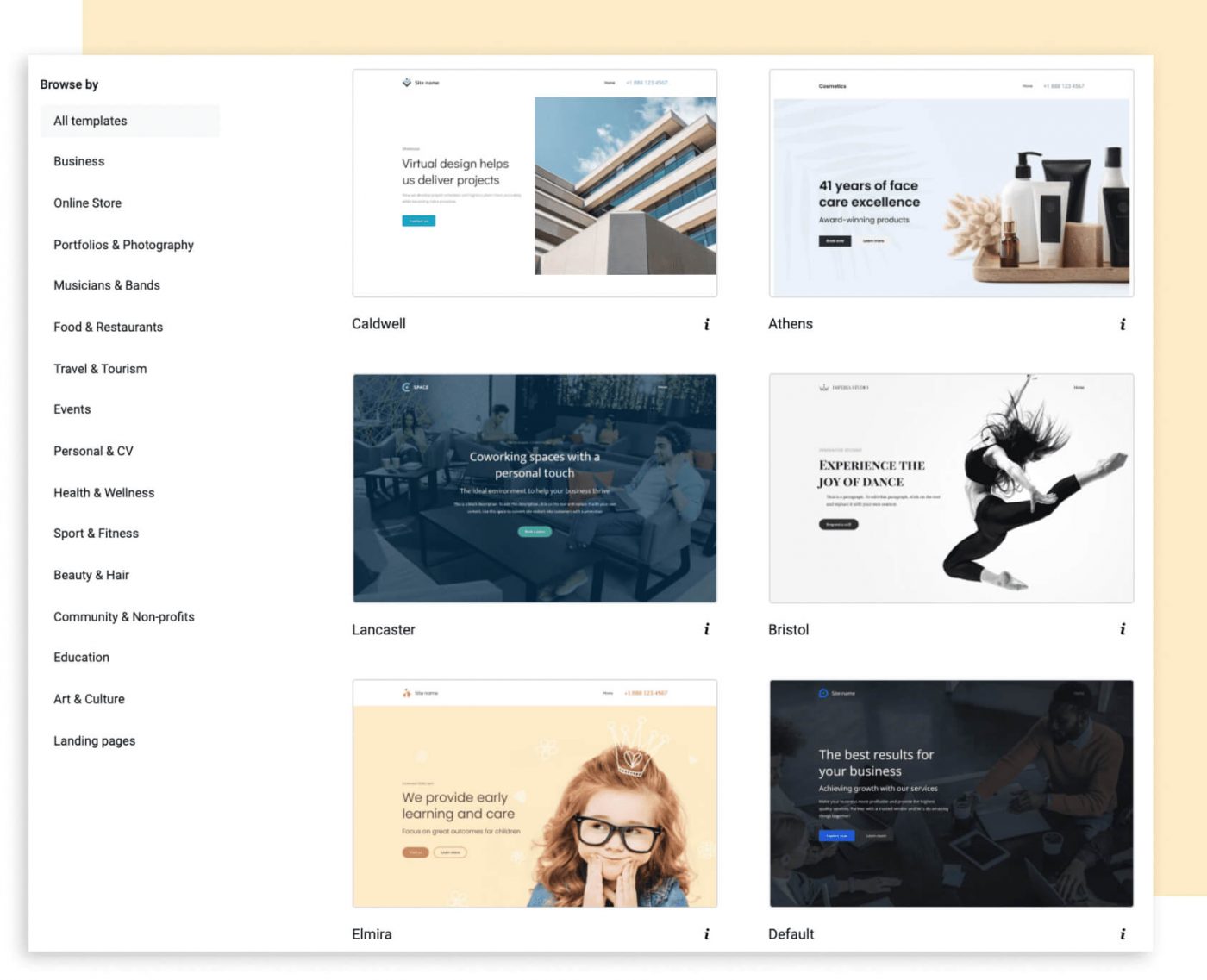
Explore Our Web Design Services website builder
Create Your Dream Website Today. Make your mark. Build your own professional website, ecommerce store, or captivating portfolio.
View Website Builder Website design services
Web Designers You Can Trust. Our expert web designers work their magic on your website, while you’re busy working your magic on growing your business.
View Website Design Services From Our Customers
Brands That Trust Hostway. Our Email & Collaboration Tools Get more done with these email and collaboration power-ups.
Exchange Work smarter with Microsoft business-class email and calendaring.
Explore Exchange Stay in the Loop Join Our Newsletter Stay ahead of the pack with the latest news, web design advice, and digital insights, delivered straight to your inbox.
24/7 support
How Can We Help You Today? Growing your web presence is tricky business, that’s why we're here to help! Our friendly support team is ready and excited to answer your questions and help you along the way.
Sales 1 (866) 680 7556 Support 1 (866) 467 8929 Send Us a Message support@hostway.com Gmail Spam Policy Update: How to Ensure your Messages are Successfully Delivered to Gmail Accounts. Learn More.